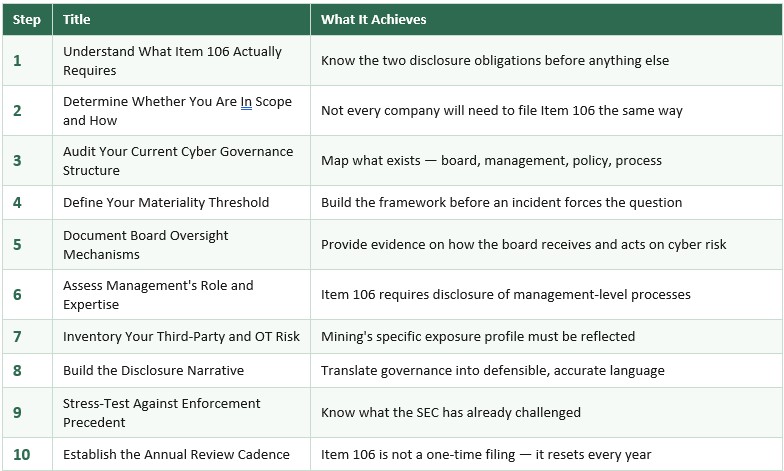
Ten Steps to SEC Regulation S-K Item 106 Readiness
What mining, resource companies, oil and gas and defense-adjacent companies need to know about cybersecurity governance disclosure — before the filing sprint begins ion.
5/12/202610 min read
Most pre-IPO resource companies don't realize they have a cybersecurity disclosure gap until the filing sprint begins. By then, the options narrow considerably. Remediation under time pressure becomes a liability — something that has to be disclosed rather than something that demonstrates governance maturity. Investors and underwriters and the SEC notice as well.
Item 106 of Regulation S-K, introduced under the SEC's 2023 cybersecurity disclosure rules, requires public companies to disclose two things annually: how their board of directors oversees cybersecurity risk, and how management assesses, identifies, and manages that risk.
It sounds procedural but in practice, it is one of the most consequential governance questions on the registration statement.
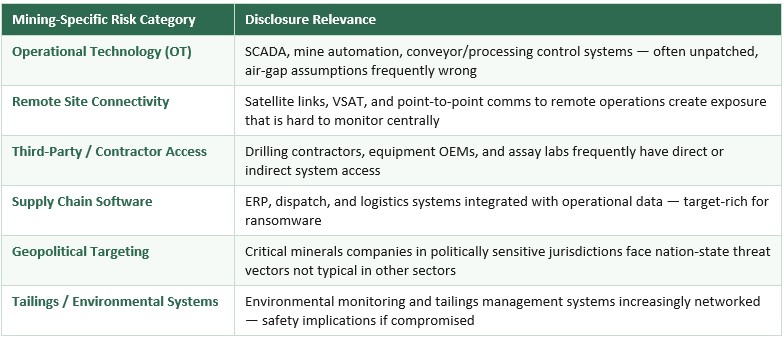
The mining, resource and defense-adjacent sectors have a specific exposure profile that makes this harder than it appears. Operational technology environments, remote site connectivity, geopolitical threat vectors, and third-party contractor access create a risk landscape that is meaningfully different from a software company or a financial services firm.
The disclosure framework was probably not written with that complexity in mind. The ten steps below are designed to help companies in these sectors navigate it — not during the filing sprint, but well before it. A quote that resonates is, "Skate to where the puck is going, not where it has been." — Wayne Gretzky.
STEP 1 Understand What Item 106 Actually Requires
Before you can assess your readiness, you need to understand precisely what the rule requires — because it is frequently mischaracterized as a general cybersecurity disclosure obligation when it is actually multiple obligations with different governance and disclosure implications:
- Item 106(b) requires disclosure of the company’s processes for assessing, identifying, and managing material cybersecurity risks, including whether those risks have materially affected or are reasonably likely to materially affect the company’s strategy, operations, or financial condition.
- Item 106(c) focuses on governance. Companies must disclose the board’s oversight of cybersecurity risk and management’s role in assessing and managing material cybersecurity threats.
To be clear, risk management and strategy requirements are critical. SEC Item 106 requires disclosure of processes for assessing, identifying, and managing material risks including cybersecurity risks, plus whether cyber risks that have materially affected or are reasonably likely to affect the company.
Critically, Item 106 is an annual disclosure requirement in the Form 10-K (or 20-F for foreign private issuers). It is not a one-time IPO filing obligation. Whatever governance structure you describe in your registration statement, you will need to describe — and maintain — in every subsequent annual filing.
STEP 2 Determine Whether You Are In Scope — and How
If you are filing a Form S-1 or F-1 registration statement for a US IPO, Item 106 applies. If you are a foreign private issuer filing on Form 20-F, the equivalent disclosure requirements apply under that form. If you are a smaller reporting company, you have access to scaled disclosure accommodations — but Item 106 still applies in substance.
For mining companies with dual listings, cross-border considerations matter. A company listed on the TSX or ASX that is also pursuing a US listing must reconcile its existing governance disclosure with Item 106's specific requirements. The two frameworks are not identical, and the gap between them is often where the work lies.
Understanding your filing form and company classification before you begin building the governance structure is essential — because the disclosure accommodations available to smaller reporting companies are meaningfully different from those available to accelerated filers, and building toward the wrong standard wastes time and creates gaps.
STEP 3 Audit Your Current Cyber Governance Structure
The audit is a great starting point. Before you can build toward Item 106 readiness, you need an accurate picture of what currently exists — at the board level, at the management level, and in the documented policies and processes that support both.
Some questions to ask:
- At the board level: Does the board receive cyber risk reporting? Which committee oversees it — audit, risk, or a dedicated technology committee? How frequently? In what format? Who presents? What decisions have been made based on that reporting?
- At the management level: Is there a named individual or function responsible for cybersecurity risk management? What is their reporting line? What processes exist for identifying and escalating material risks? What is the evidence that those processes operate as described?
- At the policy and process level: What documentation exists? When was it last reviewed? Is it current relative to the company's actual operating environment — including any recent acquisitions, site expansions, or technology changes?
The audit will surface gaps and that is its purpose. A gap identified at this stage is a remediation opportunity. A gap identified during SEC comment letter review is a disclosure problem.
STEP 4 Define Your Materiality Threshold
Item 106 requires disclosure of how the company identifies and manages material risks from cybersecurity threats. The word material is doing significant work in that sentence. If you consider honestly the companies individual appetite for risk early on this will lead to easier solutions later on. The SEC's definition of materiality for cybersecurity purposes is the same as its general definition: information is material if there is a substantial likelihood that a reasonable investor would consider it important.
For companies operating in the highlighted sectors, the materiality question has several dimensions.
- Visualize a matrix with likelihood one axis and impact on the other.
An operational disruption at a single site may or may not be material depending on the company's production concentration. A breach involving contractor access to geological data may be material if that data has competitive value. A ransomware event affecting ERP systems is material if it affects financial reporting or production scheduling at scale.
The materiality determination framework should be built before an incident forces the question — because under Item 1.05 of Form 8-K, a public company must disclose a material cybersecurity incident within four business days of determining materiality. That determination must happen fast, under pressure, and it must be defensible.
To be clear, Item 106 requires accurate governance disclosure, not disclosure of sensitive technical vulnerabilities that would materially increase operational risk.
STEP 5 Document Board Oversight Mechanisms
Item 106(b) is where companies can face their first gap, specifically related to risk management and strategy. Board-level cyber oversight in the mining, resource and defense-adjacent sectors have historically been informal — maybe a periodic briefing from the IT function, an occasional agenda item at the audit committee, a risk register that includes cyber without specific governance accountability.
What Item 106(b) requires you to describe is a risk management strategy and mechanism: a structure through which the board receives, considers, and acts on cybersecurity risk information. The description must be accurate. If the mechanism is an audit committee quarterly briefing with a standing agenda item and a defined escalation protocol, you can describe that. If the mechanism is an annual CEO update without a structured framework, you need to describe that accurately — or build something more robust before you file.
The documentation work here involves three things: formalizing the governance structure if it does not already have defined parameters, creating a record of board engagement with cyber risk that predates the filing, and ensuring the individuals presenting cyber risk to the board has sufficient expertise to make the reporting meaningful.
One important nuance for mining and resources companies with non-executive directors drawn primarily from technical and operational backgrounds: the board does not need to have cybersecurity experts. It needs to have processes and procedures through which cyber risk is surfaced, understood, and acted upon and where questions can be answered. The disclosure should reflect the process; not claim expertise the board does not have.
STEP 6 Assess Management's Role and Expertise
Item 106(c) is governance and requires disclosure of management's role in assessing, identifying, and managing material cybersecurity risks. Specifically, the SEC expects companies to describe whether the individuals or committees responsible for this function have relevant expertise — and if so, the nature of that expertise.
For a pre-IPO mining company, this question often surfaces an uncomfortable reality: cybersecurity risk management has potentially been handled by IT operations personnel without a formal management-level accountability structure. As an example, the individual responsible for patching servers is not the same as a management function that identifies, assesses, and escalates material cyber risks to the board.
The remediation here is structural. It involves defining a named management-level function or individual with documented accountability for cyber risk management, establishing the reporting line between that function and the board oversight mechanism from Step 5, and ensuring the expertise claim in the disclosure is supportable.
Expertise can be established through credentials, experience, or supported through external advisors and third-party assessments. The disclosure must accurately reflect how expertise is obtained and applied — not simply assert that management has relevant expertise without a basis for the claim.
STEP 7 Inventory Your Third-Party and OT Risk — Mining's Specific Exposure
Most cybersecurity disclosure frameworks were developed around enterprise information systems. Mining and resource companies operate industrial systems, contractor ecosystems, remote communications infrastructure, and safety-critical environments simultaneously.
Understanding and accurately disclosing that profile is one of the most important — and most frequently underestimated — elements of Item 106 readiness for mining companies.
For each of these risk categories, Item 106 readiness requires two things: a process for identifying and assessing the risk, and a governance mechanism through which material risks are escalated and managed. The disclosure must reflect the actual process — not an aspirational one.
Third-party risk is particularly acute in the mining sector. Rio Tinto's 2023 breach came through a third-party file transfer tool. Northern Minerals' 2024 incident occurred in a geopolitically charged context hours after a government divestment order. These are not hypothetical scenarios — they are sector-specific threat patterns that Item 106 disclosures should reflect.
If your company does not have a formal third-party cyber risk assessment process, that gap should be remediated before filing — and the remediation should generate documentation that predates the registration statement, not documentation created in response to underwriter diligence.
STEP 8 Build the Disclosure Narrative
Once the governance structure exists and is documented, the work of translating it into Item 106 disclosure language begins. This is not a legal drafting exercise that can be handed entirely to counsel. It requires the people who understand the governance structure to work with counsel to ensure the disclosure is accurate, complete, and not misleading.
The disclosure narrative for Item 106 should cover four elements for board oversight: which body has oversight responsibility, how cyber risk is reported to that body, the frequency and nature of reporting, and how the board engages with management on cybersecurity matters.
For management's role, the narrative should cover: the process for identifying and assessing cybersecurity risks, how material risks are escalated, the expertise of the individuals responsible, and how third-party and external risk is incorporated into the assessment process.
The most common drafting error is abstraction — language that describes governance in general terms that could apply to any company rather than specific mechanisms that reflect this company's actual structure. The SEC's comment letter practice targets generic disclosure. Specificity is protective.
STEP 9 Stress-Test Against Enforcement Precedent
Before finalizing the Item 106 disclosure, it should be stress-tested against the SEC's actual enforcement and comment letter record — because the SEC has been clear about what it considers inadequate, and that precedent is the most useful calibration tool available.
The SEC's 2024 action against SolarWinds and its CISO Timothy Brown is the most significant enforcement reference point. The SEC case was dismissed with prejudice in 2025, while the July 2024 opinion still offers useful lessons on misleading cyber statements. https://www.nysd.uscourts.gov/sites/default/files/2024-07/SolarWinds%20Opinion%20%28Dkt.%20125%29.pdf
The stress-test question for each element of your Item 106 disclosure is: if the SEC asked us to support this statement with evidence, could we produce that evidence within a reasonable timeframe? If the answer is no, the statement needs to be revised, or the governance needs to be built.
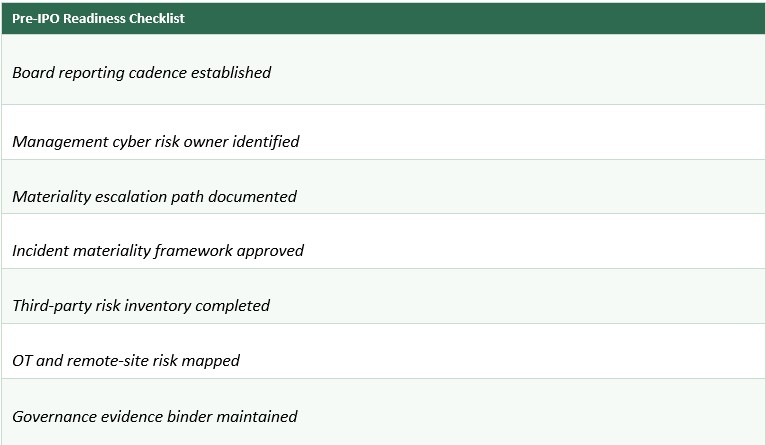
STEP 10 Establish the Annual Review Cadence
Item 106 is an annual filing obligation. The governance structure you describe in your registration statement or first annual report must be maintained, updated, and accurately disclosed in every subsequent 10-K or 20-F. This is not a one-time exercise — it is a governance discipline that resets every year.
The annual review cadence should include: a formal review of the board oversight mechanism to confirm it is operating as disclosed, a management-level assessment of whether the processes described in Item 106(c) governance, remains current and accurate, an update to the materiality framework from Step 4 to reflect any changes in the company's operating environment or threat landscape, and a review of any cybersecurity incidents or near-misses that occurred during the year and their implications for the disclosure.
For mining, resource and defense-adjacent companies that are growing through acquisition or expanding into new jurisdictions, the annual review must also assess whether the Item 106 disclosure accurately reflects the expanded scope. A governance structure that was adequate for a single-asset explorer may not be adequate for a multi-asset producer with operations across three continents.
The annual review should be documented, presented to the board audit committee, and its conclusions should inform both the updated Item 106 disclosure and any changes to the governance structure required to maintain accuracy.
The governance work required for Item 106 readiness is not burdensome if it is started early and lays the important ground work to make hard decisions potentially easier in the future. A board oversight mechanism, a management accountability structure, a materiality determination framework, and a documented third-party risk process — these are governance investments that have value independent of the filing obligation. They make the company more resilient, more credible to institutional investors, and more defensible if an incident occurs.
The companies that struggle are the ones that arrive at the S-1 or F-1 drafting session without this infrastructure in place and attempt to construct it in the weeks before filing. Form S-1/F-1 disclosure may incorporate Item 106-type disclosure through registration statement requirements, but Item 106 itself is an annual-report disclosure framework.
At that point, the governance is being built for disclosure, not for management — and sophisticated investors and SEC reviewers can tell the difference.
The pre-IPO window — typically eighteen to twenty-four months before the expected listing date — is the right time to conduct the audit in Step 3, build the structures in Steps 4 through 7, and begin generating the documented record of governance activity that makes the disclosure in Step 8 accurate and supportable.
By the time the filing sprint begins, Item 106 should be a description of what already exists — not a construction project running on the critical path.
Sturnella's Role
Sturnella advises mining, energy, infrastructure, and defense-adjacent companies on IPO cybersecurity readiness, SEC Regulation S-K Item 106 compliance, cyber diligence in M&A transactions, and board-level cybersecurity governance — before and during capital markets events.
We operate at the deal table, not inside the IT department. Our work is focused on governance precision, disclosure defensibility, and transaction protection.
contact@sturnellahq.com | sturnellahq.com
Disclaimer: This article appeared on the Sturnella website at sturnellahq.com and is provided for informational purposes only. It does not constitute investment advice, financial advice, legal advice, or a solicitation to buy or sell any security or financial instrument. The information contained herein is based on publicly available sources and is believed to be accurate at the time of publication but is not guaranteed. Sturnella LLC is a capital markets cybersecurity and governance advisory firm and is not a registered investment adviser, broker-dealer, or financial institution. Always consult a qualified financial, legal, or investment professional before making any investment decision.
Contact
Reach out for discreet advisory support
contact@Sturnellahq.com
Sturnella LLC © 2026 All rights reserved.
Independence
Governance Precision
Discretion
Capital Markets Alignment
Accountability